Memory forensics is becoming an essential aspect of digital forensics and incident response. When a system is believed to have been compromised or infected, the analyst needs a convenient way to take a memory image of the host. DumpIt, a tool from Comae Technologies, enables this.
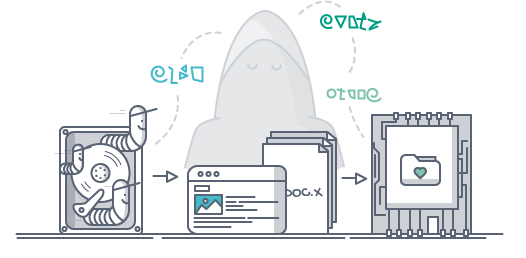
The user can then provide the analyst the USB key which will contain the memory image file. The analyst can use Comae Stardust or Microsoft WinDbg to analyze the images and look for malicious artifacts.
DumpIt provides a convenient way of obtaining a memory image of a Windows system even if the analyst is not physically sitting in front of the target computer. It’s so easy to use, even a non-technical user can do it.
DumpIt For Linux is now also available and works great on Cloud Infrastructure (Microsoft Azure, Amazon Web Services, Google Cloud Platform). It comes in a Docker image, which makes it easy for analysts to deploy. Its command line interface allows users to send the Linux images to Comae Cloud or for storing on your infrastructure managed by other cloud providers, such as Azure, Amazon, or Google Cloud Platform.